Guide
Use SSH keys to authenticate with your SFTP server and ensure you are connecting to the correct server.
Because SFTP is built on top of SSH, you can use SSH keys to authenticate with the server, instead of passwords. The full details of configuring your SFTP server to use keys for authentication is beyond the scope of this help doc, but you will create a pair of keys - one public and one private. The public key will be placed on the server and the private key will be given to EasyFTP. EasyFTP will then use the private key when connecting to your SFTP server.
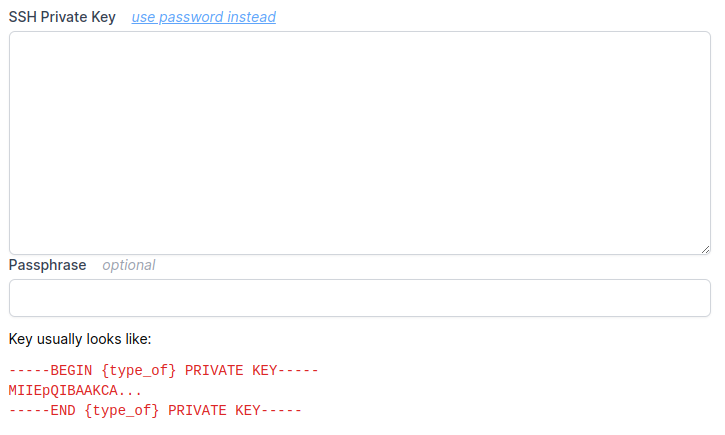
If your private key is encrypted with a passphrase, EasyFTP will also need that passphrase.
When connecting to your SFTP server, EasyFTP can be configured to verify the server's host key. This can prevent man-in-the-middle spoofing attacks, where a different server - pretending that it is your SFTP server - intercepts traffic. To enable host key verification, you will need to supply EasyFTP with the server's public key. EasyFTP can accept the contents of an OpenSSH .pub file or the relevant line from a .ssh/known_hosts file.
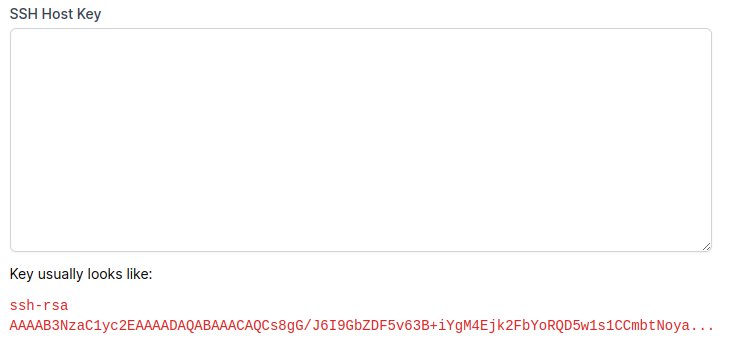
Should the SFTP's host key ever not match the host key stored in EasyFTP, we will refuse to connect to the server. Note that a server's host key can change if it is upgraded or migrated between computers. In these cases, you will need to edit the EasyFTP connection and supply the new host key.
Copyright © 2026. All rights reserved.